5 ChatGPT Tips You Should Stop Using Right Now
By Deepti Pathak Over the last year, ChatGPT has become one of the most utilized tools for writing, research,…
The post 5 ChatGPT Tips You Should Stop Using Right Now appeared first on Fossbytes.
Source:: Fossbytes
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
New Spotify Update Helps You Track Your Music Weekly
By Deepti Pathak Music tastes can change every week, and Spotify has just made it easier to keep track…
The post New Spotify Update Helps You Track Your Music Weekly appeared first on Fossbytes.
Source:: Fossbytes
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
14 ways IT can keep ahead of (and integrate) innovative tech
In case you hadn’t noticed, change is in the air.
Over the past few years, every day seemingly brings new tales of how businesses are still trying to integrate generative AI (genAI) tools, figure out what agentic AI can do for them, and decipher what genAI firms are really saying about the new features they routinely unveil.
There are ongoing reports that augmented or virtual reality really does have a future in the business world, AI PCs will take over the PC market in a post Windows 10 world, Arm-based PCs will change everything, and Apple has moved into the enterprise space faster than expected.
There’s a lot going on in the enterprise tech world. Add all those changes to the day-to-day standard IT job of keeping everything up running and many IT leaders and professionals can quickly get overwhelmed.
So how do you keep up?
Here are 14 ways IT departments can approach this conundrum while maintaining their sanity amid constant change — especially with everyone from the C-suite to front-line workers clamoring for the latest tech.
Set expectations. Be clear about what you can realistically accomplish in terms of new technology given your budget and manpower. Set firm boundaries and be consistent both within and outside the IT department.
Rely on trusted sources for research. Cultivate tech news sources you can rely on. Many tech developments, especially around hot topics like genAI, are routinely covered by a variety of media sources (including mainstream news outlets and tech influencers). Separate the hype from what is really going on — what’s working and what isn’t.
Communicate with peers. In addition to curating sources, having relationships with people at other organizations in your industry (and sometimes outside your industry) is a powerful way to see what colleagues are doing and get perspective. This can help lead to innovations within your IT department, opportunities for collaboration, and potential new hires.
Be open to suggestions. Being receptive to ideas inside and outside IT can be critical. No IT leader or admin is an expert on everything when it comes to emerging technology. Good ideas can come from anywhere, so it’s important to demonstrate your openness. (Not every idea will be worth pursuing, of course.)
Open proofs of concept. When ideas seem attainable and worth exploring in depth, proof-of-concept projects is a logical next step. Each should be well defined, have set timelines and measurable goals. If projects are open ended or vaguely planned, they risk becoming zombie projects that never die.
Realize not everything will work. That’s why proofs of concept and pilot projects are important. Be prepared for failure. Many if not most ideas or projects, will fail or at least go through a rough patch. But even failures can be useful learning experiences. Set expectations accordingly.
Encourage experimentation, but with guardrails. Experimentation is a good thing, be it by technical staff, executives, or everyday users. You do yourself a disservice by outlawing experimentation, but you can’t let it go unchecked. Whether for security reasons, IT resource limits or usability/user training requirements, you need to keep experiments from overtaking everything else need to do.
Shadow IT exists; use it. For years, studies have shown that shadow IT — where users quietly build their own workflows and processes and even make their own purchases without informing IT— is more prevalent than many decision makers realize. With almost any new technology, users will experiment, with or without IT’s knowledge. (This is how BYOD began.) Your best approach is to allow this to happen, and in some circumstances encourage it. Banning it isn’t an effective strategy and you might actually learn how to incorporate various tools and techniques into larger, more managed, projects.
If you say no, explain why. There’s an old adage that IT is the department of “no,” always shutting down people and ideas. Even if you’re ok with shadow IT projects, there will be times you have to draw a line. Few people like being told no, it but if you can explain your rationale, most will accept it. (Whatever idea you’ve vetoed could still reemerge in the shadows; a solid explanation of IT’s thinking gives you an opportunity to work with those employees cooperatively.)
Work with vendors, partners and consultants. No IT department is an island. Everyone has to deal with vendors, consultants and other partners to successfully get a handle on new technologies. Outside relationships can bring forward new ideas, allow IT to see things with fresh eyes and augment your internal staff. (Beware of “partners” too focused on hype — and be certain that they understand your current position and specific enterprise needs.)
Create centers of excellence. These centers can be a good way to educate staffers, execs and front-line employees about the challenges of exploring, adopting and integrating emerging technologies. This can relieve pressure on IT leaders to be up to date on every tech development and how it relates to your company. And they can help build a working group to establish expertise, use cases, best practices and needed requirements, documentation and support.
Avoid hype. Control your enthusiasm for new technology. This doesn’t mean you don’t show enthusiasm; it does mean that you operate in a “no hype” zone, where clear eyes and realism are in order.
Remember scalability, support and security. New technologies can be exciting, but IT has to consider how each will scale, the strain they’ll place on tech support, and how they could affect corporate security. As each new concept, product or initiative arises, IT always has to keep these three areas in mind.
Be open to disruption, but be realistic. GenAI, agentic AI, AI PCs — note the AI thread running through all three — are potentially massive disruptors of the status quo. IT can’t afford to be afraid of disruption, but it’s important to remain realistic about the nuts and bolts of getting new tech initiatives working —as well as the potential affects on your organization and its workers.
A host of new technologies is coming to market faster than ever. Knowing how to evaluate them and their potential impact on your business is a requirement for every IT leader. Things will never be as simple as they once were, but you can develop pathways and processes for you, your staff and organization to manage the flood of news and announcements and separate the potential from the hype.
Because the pace of change isn’t likely to slow down anytime soon.
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Microsoft product roadmap hints at ‘Agentic Users’ with their own M365 licenses
Later this month, Microsoft plans to enhance its M365 productivity suite with “Agentic Users,” autonomous AI agents with their own identities and access to enterprise IT systems that can collaborate with one another and with humans.
“These agents can attend meetings, edit documents, communicate via email and chat, and perform tasks autonomously,” Microsoft said in an addition to its product roadmap entitled “Microsoft Teams: Discovery and Creation of Agentic Users from Teams and M365 Agent Store.” The update will be rolled out to desktop systems worldwide beginning later in November, according to the roadmap entry.
Microsoft provided further details about its plans for Agentic Users in a message posted to the Microsoft Admin Center, according to various reports from around the web.
Microsoft MVP João Ferreira posted what he said was a copy of it a copy of LC1183300 to his personal blog.
“Agentic Users are a new class of AI-powered digital entities designed to function as autonomous, enterprise-grade virtual colleagues. Unlike traditional bots, Agentic Users are provisioned as full-fledged user objects with their own identity in the organization’s directory (via Entra ID or Azure AD), email addresses, Teams accounts, and presence in the org chart,” the purported Microsoft announcement began.
All users in enterprises with access to Microsoft teams and the Microsoft 365 Copilot store will be able to view agent templates, although only approved users will be able to create agents from those templates, it continued.
Microsoft did not respond to an email seeking confirmation of the authenticity of the message.
The post also contains images that hints at the use cases these new Agentic Users might be used for, including procurement, HR initiatives such as employee wellness, tracking team tasks, and developing workflows. There was no mention, though, of how Agentic Users compare to the many agents that M365 already offers, including its Facilitator and Project Manager agents, its Office Agent, and different flavors of Copilots for sales, service, and finance operations.
Confusion over licensing, increasing costs, and Microsoft’s revenue play
Before they can create any of the new agents, admins will need to approve a template for use and “assign the required A365 license,” the posting said. No further information was included about the nature or pricing of these licenses.
Analysts speculated how the new A365 licenses might relate to existing M365 licenses, which are typically sold on a per-user, per-month basis with an annual commitment.
“Previously released agents like Facilitator or Project Manager were bundled under M365 Copilot entitlements, with advanced actions billed via Copilot credits. A365 introduces explicit per-agent licensing and admin-controlled approval through the Agent Store and separates agent costs from human seats,” said Forrester vice president and principal analyst Charlie Dai.
Alexander Golev, partner at SAM Expert, a specialist in managing Microsoft licensing and cloud costs, suggested instead that A365 will replace M365 user licenses.
“Our expectation is that it will provide a combination of user-like access to Microsoft 365 services on a monthly/annual/3-annual fee basis plus the core functionality of M365 Copilot. Additional AI use will be charged in the same manner as with users — prepaid capacities and pay-as-you-go items. We don’t expect them to be all-inclusive,” he said.
Microsoft has been changing its licensing practices to increase its revenue significantly, Golev said. “In the recent years, they moved from server- or device-based licensing to CPU-based and then core-based.”
In its reporting of M365 revenue, Microsoft focuses on average revenue per user (ARPU), “which is now hitting its ceiling,” he said. “You can only scale so far. Earth’s population grows slower than Microsoft’s revenue targets. What we have been predicting is the move to ARPA — Average Revenue per Agent, which can scale exponentially,” Golev said.
Another licensing expert, Rich Gibbons, blogged about the new A365 licenses, saying that he expected Microsoft to use them as an opportunity to generate additional consumption-based revenue.
Risk of agent sprawl?
Analyst Pareekh Jain of Jain Consulting said he expects Microsoft to update its previously introduced agents as part of the rollout of Agentic Users, giving the existing agents their own email addresses and Microsoft Entra IDs too.
“Too many autonomous agents for overlapping or redundant tasks mirror the challenges most enterprises have faced with bot and app sprawl in prior M365 deployments. Without tight governance, enterprises could face duplication, higher spend, data security exposure, and oversight challenges,” Jain said.
But, said Dai, Entra IDs could play a pivotal role in avoiding that sprawl. “These IDs can be used to treat agents as directory-backed identities enabling lifecycle control, access reviews, and compliance policies….helping enterprises gain visibility and accountability,” he said.
Even before we learn all the details of these new Agentic Users, it’s clear that there are some aspects of them to which enterprises will have to pay particular attention.
Dai pointed out to the need for effective collaboration between IT asset management and FinOps teams, while Everest analyst Tanvi Rai said enterprises will need strong change management to train employees to supervise, validate and govern agent behavior effectively.
Despite all the uncertainty, what is evident is that Microsoft’s move will further intensify the race among rivals, such as Salesforce and ServiceNow, who are also accelerating their efforts to introduce autonomous AI-driven agents aimed at boosting productivity across enterprises.
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Does talk of government backstops mean an AI bubble is about to burst?
It’s been an uncomfortable few days for AI vendors. On Friday, the big tech companies saw $1.2 trillion wiped off their market valuations, reflecting the concerns of many analysts that AI valuations are too high and the market is heading for a serious crash.
Just a few days earlier, OpenAI CFO Sarah Friar suggested that the US government could help the industry by providing a “backstop” to guarantee commercial loans financing AI chips in data centers — although hours later she took back those words in a LinkedIn post. The same day, OpenAI CEO Sam Altman also denied the company wanted government loan guarantees in a mammoth 6,000-character post on X (formerly Twitter).
So how should CIOs view the future of their own AI investments? Financial analysts have a mixed view.
According to Shawn DuBravac of the Avrio Institute, big tech customers need to be more pragmatic, but don’t need to panic. “Companies don’t need to rewrite their strategy, but market volatility is a stress test of AI investment. The large tech companies recognize that the long-term demand for AI infrastructure is very strong.
Ilya Rybchin, principal at financial advisory firm BDO USA, said that CIOs shouldn’t be worried about the technology becoming obsolete or vendors disappearing. “Customers should be worried about the anemic return on their own AI investments, irrespective of how their vendors are performing or what the media is saying about their vendors.”
Freeze AI procurement
He had some stark advice. “Companies should freeze new AI procurement. They should stop buying tools until they can prove they’re getting value from the ones they have.” He added that many companies are buying multiple AI platforms without using any effectively. “It’s like buying three chainsaws when you haven’t learned to use the first one,” he said.
Global technology futurist Daniel Burrus of Burrus Research predicted that organizations may need to rethink staffing levels. “We’re seeing a lot of layoffs due to AI investments, particularly among coders. However, I think these companies are missing a trick. I prefer to think of AI as Augmented Intelligence as it’s about augmenting, rather than replacing.
He said that there is already a change in the air. “We are seeing companies who have laid off people hiring them back.”
Concerns that the AI market is a bubble that’s about to burst won’t entirely go away. Altman has said that OpenAI is projecting an annualized revenue run rate of $20 billion this year and is committed to spending $1.4 trillion over the next eight years. Just last week, the company signed a deal with AWS for $38 billion to host its services on Amazon’s cloud service. That’s heavy investment and there will certainly be doubts whether it can grow revenue to match that expenditure.
Burrus draws parallels with Amazon.. “It took a very long time for them to make a profit but they’re racing for the intelligence to be better than a human being, and that is going to take some time.” However, Amazon didn’t make the dizzying levels of investment that OpenAI is committing itself to.
Not an extinction-level event
There is agreement, however, that the AI industry as a whole can survive without government support for one failing company.
DuBravac said, “If OpenAI stumbles, customers would feel turbulence and disruption but nothing that they couldn’t overcome.”
And Rybchin said that it could aid the progress of AI. “OpenAI failing would not be an extinction-level event for AI. On the contrary, it could be a healthy catalyst, forcing a necessary diversification of the AI landscape, encouraging competition and innovation from a wider range of players.
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Why the Ruko U11MINI 4K Is the Best Thanksgiving Gift To Capture Moments
By Hisan Kidwai When consumer drones first came about, they were extraordinarily expensive, bulky, and only suitable for filmmakers…
The post Why the Ruko U11MINI 4K Is the Best Thanksgiving Gift To Capture Moments appeared first on Fossbytes.
Source:: Fossbytes
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
What Do The Different Icons & Symbols on WhatsApp?
By Deepti Pathak WhatsApp uses several small icons and symbols to make conversations and calls handier for the user….
The post What Do The Different Icons & Symbols on WhatsApp? appeared first on Fossbytes.
Source:: Fossbytes
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Garena Free Fire (FF) Max Redeem Codes For Today: November 9
By Hisan Kidwai Free Fire Max is one of the most popular games on the planet, and for good…
The post Garena Free Fire (FF) Max Redeem Codes For Today: November 9 appeared first on Fossbytes.
Source:: Fossbytes
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Garena Free Fire (FF) Max Redeem Codes For Today: November 8
By Hisan Kidwai Free Fire Max is one of the most popular games on the planet, and for good…
The post Garena Free Fire (FF) Max Redeem Codes For Today: November 8 appeared first on Fossbytes.
Source:: Fossbytes
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Microsoft lets shopping bots loose in a sandbox
Do you think it’s time to turn an AI agent loose to do your procurement for you? As that could be a potentially expensive experiment to conduct in the real world, Microsoft is attempting to determine whether agent-to-agent ecommerce will really work, without the risk of using it in a live environment.
Earlier this week, a team of its researchers launched the Magentic Marketplace, an initiative they described as an “an open source simulation environment for exploring the numerous possibilities of agentic markets and their societal implications at scale.” It manages capabilities such as maintaining catalogs of available goods and services, implementing discovery algorithms, facilitating agent-to-agent communication, and handling simulated payments through a centralized transaction layer.
The 23-person research team wrote in a blog detailing the project that it provides “a foundation for studying these markets and guiding them toward outcomes that benefit everyone, which matters because most AI agent research focuses on isolated scenarios — a single agent completing a task or two agents negotiating a simple transaction.”
But real markets, they said, involve a large number of agents simultaneously searching, communicating, and transacting, creating complex dynamics that can’t be understood by studying agents in isolation, and capturing this complexity is essential “because real-world deployments raise critical questions about consumer welfare, market efficiency, fairness, manipulation resistance, and bias — questions that can’t be safely answered in production environments.”
They noted that even state-of-the-art models can show “notable vulnerabilities and biases in marketplace environments,” and that, in the simulations, agents “struggled with too many options, were susceptible to manipulation tactics, and showed systemic biases that created unfair advantages.”
Furthermore, they concluded that a simulation environment is crucial in helping organizations understand the interplay between market components and agents before deploying them at scale.
In their full technical paper, the researchers also detailed significant behavioral variations across agent models, which, they said, included “differential abilities to process noisy search results and varying susceptibility to manipulation tactics, with performance gaps widening as market complexity increases,” adding, “these findings underscore the importance of systematic evaluation in multi-agent economic settings. Proprietary versus open source models work differently.”
Bias and misinformation an issue
Describing Magentic Marketplace as “very interesting research,” Lian Jye Su, chief analyst at Omdia, said that despite recent advancements, foundation models still have many weaknesses, including bias and misinformation.
Thus, he said, “any e-commerce operators that wish to rely on AI agents for tasks such as procurement and recommendations need to ensure the outputs are free of these weaknesses. At the moment, there are a few approaches to achieve this goal. Guardrails and filters will enable AI agents to generate outputs that are targeted and balanced, in line with rules and requirements.”
Many enterprises, said Su, “also apply context engineering to ground AI agents by creating a dynamic system that supplies the right context, such as relevant data, tools, and memory. With these tools in place, an AI agent can be trained to behave more similarly to a human employee and align the organizational interests.”
Similarly, he said, “we can therefore apply the same philosophy to the adoption of AI agents in the enterprise sector in general. AI agents should never be allowed to behave fully autonomously without sufficient check and balance, and in critical cases, human-in-the-loop.”
Thomas Randall, research lead at Info-Tech Research Group, noted, “The key finding was that when agents have clear, structured information (like accurate product data or transparent listings), they make much better decisions.” But the findings, he said, also revealed that these agents can be easily manipulated (for example, by misleading product descriptions or hidden prompts) and that giving agents too many choices can actually make their performance worse.
That means, he said, “the quality of information and the design of the marketplace strongly affect how well these automated systems behave. Ultimately, it’s unclear what massive value-add organizations may get if they let autonomous agents take over buying and selling.”
Agentic buying ‘a broad process’
Jason Anderson, vice president and principal analyst at Moor Insights & Strategy, said the areas the researchers looked into “are well scoped, as there are many different ways to buy and sell things. But, instead of attempting to execute commerce scenarios, the team kept it pretty straightforward to more deeply understand and test agent behavior versus what humans tend to assume naturally.”
For example, he said, “[humans] tend to narrow our selection criteria quickly to two or three options, since it’s tough for people to compare a broad matrix of requirements across many potential solutions, and it turns out that model performance also goes down when there are more choices as well. So, in that way there is some similarity between humans and agents.”
Also, Anderson said, “by testing bias and manipulation, we can see other patterns such as how some models have a bias toward picking the first option that met the user’s needs rather than examining all the options and choosing the best one. These types of observations will invariably end up helping models and agents improve over time.”
He also applauded the fact that Microsoft is open sourcing the data and simulation environment. “There are so many differences in how products and solutions are selected, negotiated, and bought from B2B versus B2C, Premium versus Commodities, cultural differences and the like,” he said. “An open sourcing of this tool will be valuable in terms of how behavior can be tested and shared, all of which will lead to a future where we can trust AI to transact.”
One thing this blog made clear, he noted, “is that agentic buying should be seen as a broad process and not just about executing the transaction; there is discovery, selection, comparison, negotiation, and so forth, and we are already seeing AI and agents being used in the process.”
However, he observed, “I think we have seen more effort from agents on the sell side of the process. For instance, Amazon can help someone discover products with its AI. Salesforce discussed how its Agentforce Sales now enables agents to help customers learn more about an offering. If [they] click on a promotion and begin to ask questions, the agent can them help them through a decision-making process.”
Caution urged
On the buy side, he said, “we are not at the agent stage quite yet, but I am very sure that AI and chatbots are playing a role in commerce already. For instance, I am sure that procurement teams out there are already using chat tools to help winnow down vendors before issuing RFIs or RFPs. And probably using that same tool to write the RFP. On the consumer side, it is very much the same, as comparison shopping is a use case highlighted by agentic browsers like Comet.”
Anderson said that he would also “urge some degree of caution for large procurement organizations to retool just yet. The learnings so far suggest that we still have a lot to learn before we see a reduction of humans in the loop, and if agents were to be used, they would need to be very tightly scoped and a good set of rules between buyer and seller be negotiated, since checking ‘my agent went rogue’ is not on the pick list for returning your order (yet).”
Randall added that for e-commerce operators leaning into this, it is “imperative to present data in consistent, machine-readable formats and be transparent about prices, shipping, and returns. It also means protecting systems from malicious inputs, like text that could trick an AI buyer into making bad decisions —the liabilities in this area are not well-defined, leading to legal headaches and complexities if organizations question what their agent bought.”
Businesses, he said, should expect a future where some customers are bots, and plan policies and protections, accordingly, including authentication for legitimate agents and rules to limit abuse.
In addition, said Randall, “many companies do not have the governance in place to move forward with agentic AI. Allowing AI to act autonomously raises new governance challenges: how to ensure accountability, compliance, and safety when decisions are made by machines rather than people — especially if those decisions cannot be effectively tracked.”
Sharing the sandbox
For those who’d like to explore further, Microsoft has made Magentic Marketplace available as an open source environment for exploring agentic market dynamics, with code, datasets, and experiment templates available on GitHub and Azure AI Foundry Labs.
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Microsoft to move Configuration Manager to annual release cadence in ‘26
Configuration Manager will move to an annual release schedule while Microsoft focuses on Intune as the long-term platform for device management.
The new release schedule will begin September 2026, with version 2609, Microsoft announced in a blog post this week. Further releases will then align with the Windows security and stability update cycle (H2). Microsoft has already briefed customers on the new approach at events and in discussions; this week’s announcement makes those plans official.
The shift means that hotfix rollups will only be provided when “absolutely necessary,” such as for critical security or functionality problems, Microsoft said, with other updates coming in the annual release.
Configuration Manager, which launched in 1994 as Systems Management Server (SMS), and later rebranded to System Center Configuration Manager (SCCM), is an on-premise application that supports management of PCs and servers. Now part of the Microsoft Intune suite, it coexists and overlaps with the Intune app, a cloud-based endpoint management service.
Microsoft will continue to support Configuration Manager, with a focus on “security, stability, and long-term support,” said Danny Guillory, senior program manager at Microsoft. Any changes or deprecations “will be communicated well in advance,” he said.
Meanwhile, the Intune suite will receive “all future investments and innovation,” as Microsoft prioritizes its device management suite going forward.
“This isn’t the end of Configuration Manager, but it’s a clear signal of Microsoft’s cloud-first strategy,” said Daniel Engberg, principal consultant at Agdiwo.
Although there’s no immediate pressure to abandon Configuration Manager, organizations should start planning for “co-management or eventual migration to Intune,” he said.
Many organizations still rely heavily on Configuration Manager for on-premises and hybrid scenarios, and it remains a mature and highly capable product, according to Engberg. Furthermore, it’s not a direct replacement for Intune. “ConfigMgr does far more than just manage mobile endpoints, including robust server management and advanced deployment capabilities,” he said.
For some customers, such as those in regulated environments or that run complex infrastructure, it could make sense to remain on Configuration Manager for the foreseeable future. “In many ways, it feels like Configuration Manager is moving toward a Long-Term Servicing Channel (LTSC)-style role, focused on stability rather than new features,” said Engberg.
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Microsoft creates a team to make ‘humanist superintelligence’
“What kind of AI does the world really want?”. So begins a blog post by Mustafa Suleyman, director of AI at Microsoft. In his opinion, “it’s probably the most important question of our time.”
Suleyman recalls the progress experienced in recent years, which “has been phenomenal.” “We are breezing past the great milestones. The Turing test, a guiding inspiration for many in the field for 70 years, was effectively passed without any fanfare and hardly any acknowledgement. With the arrival of thinking and reasoning models, we’ve crossed an inflection point on the journey towards superintelligence. If AGI [artificial general intelligence] is often seen as the point at which an AI can match human performance at all tasks, then superintelligence is when it can go far beyond that performance,” he continues.
However, Suleyman advocates that the time has come to think carefully about the purpose of the technology, “what we want from it, what its limitations should be, and how we’re going to ensure that this incredible tech always benefits humanity,” rather than “endlessly debating capabilities or timing.” Accordingly, Microsoft has created the MAI Superintelligence team, led by Suleyman himself, as part of Microsoft AI. In his words, “We want it to be the world’s best place to research and develop AI, bar none. I think about it as humanist superintelligence to clearly indicate this isn’t about some directionless technological goal, an empty challenge, a mountain for its own sake. We are doing this to solve real concrete problems and do it in such a way that it remains grounded and controllable. We are not building an ill-defined and ethereal superintelligence; we are building a practical technology explicitly designed only to serve humanity.”
Suleyman is clear that this AI has extraordinary capabilities, but is specific, contained and aligned with human values. A technology that, in his view, does not seek to create autonomous and unlimited entities, but systems designed to solve real problems — such as healthcare, clean energy or education — while keeping human control as a priority. “We want to both explore and prioritize how the most advanced forms of AI can help keep humanity in control while at the same time accelerating our path towards tackling our most pressing global challenges,” he says.
What’s more, Microsoft’s head of AI says the company rejects the narrative of a “race to AGI,” which has dominated the technology discourse. Instead, he proposes a more humanist and collaborative approach, focused on tangible and lasting benefits. Technology, he argues, must continue to be an engine of moral and material progress, but guided by the conviction expressed by Albert Einstein: “The concern for man and his destiny must always be the chief interest of all technical effort.”
In Suleyman’s view, one of the key challenges is the containment and alignment of advanced systems: “Since this kind of superintelligence can continuously improve itself, we’ll need to contain and align it not just once, but constantly, in perpetuity.”
Suleyman identifies three areas where humanist superintelligence could have a transformative impact. The first is the personal AI companion, designed to assist people in their learning, productivity and well-being, without replacing human connection. The second is medical superintelligence, capable of delivering expert-level diagnostics and treatment, expanding global access to healthcare. And the third, clean and abundant energy, where AI would facilitate scientific discovery, resource optimization and development of sustainable generation technologies.
This, in his view, implies a clear set of rules if this model is to be achieved, as well as international cooperation and transparency. Suleyman says Microsoft recognizes the risk of less safe models advancing faster, so he calls for collective action to prevent innovation from being imposed without ethical control. “We are not building a superintelligence at any cost, with no limits,” he emphasizes.
Ultimately, Microsoft’s AI chief argues that humanist superintelligence seeks to keep humans at the center of the technological equation. As such, Microsoft is clear that AI must be subordinate, controllable and aligned with human values, and that its purpose is not to replace people, but to amplify their capabilities. “Superintelligence could be the best invention ever, but only if it puts the interests of human beings above everything else,” he says.
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Nikkei’s Slack breach leaks sensitive data from more than 17,000 users
Japanese media company Nikkei has confirmed that a security breach of its Slack accounts has potentially leaked highly sensitive information from more than 17,000 of its users. Consultants point to the incident as yet another reminder of the dangers when non-corporate devices are allowed to access confidential corporate data.
“An employee’s personal computer was infected with a virus, leading to the leakage of Slack authentication credentials. It is believed that this information was used to gain unauthorized access to employee accounts,” Nikkei said in a published statement. “The incident was identified in September and countermeasures such as changing passwords were implemented. Potentially leaked information includes the names, email addresses, and chat histories for 17,368 individuals registered on Slack.”
The Nikkei statement added “Considering the incident’s significance and to ensure transparency, we voluntarily reported it to [Japan’s] Personal Information Protection Commission. No leakage of information related to sources or reporting activities has been confirmed.”
Cybersecurity consultant Brian Levine, a former federal prosecutor who today serves as executive director of FormerGov, a directory of former government and military specialists, stressed that this is part of an ongoing trend of Slack breaches.
“There is often increased risk when employees or contractors access company resources from non-company-managed devices. Recent attacks against Okta, MGM Resorts, and others have been linked to such unmanaged access,” Levine said, adding that last year, “an attacker exfiltrated more than [1 terabyte] of internal data from Disney’s Slack environment when a contractor had accessed Slack from an unmanaged device, bypassing monitoring tools.”
Erik Avakian, technical counselor at Info-Tech Research Group, noted that one of the most concerning things about attacks similar to the Nikkei breach is that the attackers are often able to easily bypass MFA defenses.
“An employee’s computer gets hit by malware designed to steal credentials. The malware grabs Slack session tokens and cookies, then sends them to attacker command and control servers,” Avakian said. “With those stolen and likely active tokens, the attacker is able to log into Slack from their own device and access private channels and chat history without even triggering a multi-factor authentication prompt, since they reused an already-authenticated session.”
Avakian said that the nature of these attacks suggests that enterprise CISOs should consider procedural changes.
This kind of attack would give threat actors “broad access to channels and integrations, which made the impact worse. Weaknesses around this incident shine a light on unmanaged or poorly protected devices, long-lived tokens, and not enough logging or alerts for suspicious sessions,” Avakian said. “Organizations can learn from these types of incident, and those using Slack, or any other widely used communications platform similar to Slack, should maintain a policy for revoking active sessions and refreshing tokens for affected users routinely, forcing password resets and rotating API tokens.”
Jeff Man, a senior information security consultant with Online Business Systems, pointed out, “the larger discussion should be on the failings of the Nikkei IT/IS program to protect against some sort of attack that targeted its employees. Why are employees allowed to use Slack on personal devices?”
“So this is really an issue of risk management,” Man said. “In the case of Nikkei, it appears the exploitation was elsewhere [on the system]. The initial access allowed the miscreants to use credentials to gain access to Slack. That’s not a compromise of Slack itself, that’s a compromise of employee account authentication.”
Stephen Boyce, security consultant and CEO of The Cyber Dr., said the Nikkei incident represents “what happens when someone uses a personal device to get into work systems. Once that device gets hit with malware, it’s game over for the credentials. The part that worries me is this could happen anywhere. People forget how much sensitive stuff ends up in Slack: messages, files, links, sometimes even credentials. Once someone has that, they can poke around pretty freely.”
“To me, it’s just another reminder that zero trust has to go all the way out to the edge, not just the network. You’ve got to know the device, use MFA tied to managed hardware, and control what data lives in those SaaS tools,” Boyce said. “You may be also asking ‘Well, do we do away with BYOD all together?’ And the short answer is ‘no’ but we do need to look at ways we can secure the workforce beyond company issued assets.”
This article originally appeared on CSO Online.
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Apple’s war in Europe
Some say good government is less government. Others have a different point of view. But the least you should be able to expect from any kind of governance is that following one law doesn’t force you to break another. That is, unless you’re Apple and the laws are made in Europe.
In a letter seen by Computerworld, Apple Vice President Kyle Andeer has come out swinging against yet another investigation into the company’s business. Apple faces a pair of inquiries under Europe’s Digital Services Act (DSA), a sprawling piece of legislation that pretends to make the online world safer and probably won’t. (UK legal firm Slaughter and May offers a useful guide here.)
Apple comes out fighting
The problem is that the two investigations arguably reflect requirements made under the DSA’s companion law, the Digital Markets Act. Apple isn’t happy, and its latest furious complaint against EU regulators pulls no punches in pointing out the futile and contradictory hypocrisy in play.
“We are concerned that these new inquiries are cynical attempts to distract from the core problems caused by the Commission’s misguided DMA enforcement efforts,” the letter says.
As part of an initial investigation, the European Commission has thrown Requests for Information (RFI) at Apple. These say regulators suspect that Apple:
“Has not put in place reasonable, proportionate and effective mitigation measures tailored to this specific systemic risk [of the dissemination of illegal content related to financial scams through App Store].”
“Has not put in place appropriate and proportionate measures to ensure a high level of safety and security of minors on their service.”
Apple helpfully points to its extensive and provable track record of having put numerous protections in place to protect customers and their children, while also pointing out that the Commission has made the task far more challenging in how it applies the DMA.
Apple is the world’s safest ecosystem
“We find it difficult to square the premise of these [requests] with the Commission’s aggressive interpretation and application of the Digital Markets Act (DMA). The Commission has consistently taken positions under the DMA that undercut Apple’s ability to protect its users,” the company said.
“Apple has always focused on protecting its users from bad actors on its platforms and in its App Store. For almost two decades, we have been investing heavily in systems and processes to identify risks of financial scams, apps that could potentially harm children, and other apps that we believe pose risks to our users on iOS and iPadOS. We have taken a number of steps to protect our users from harm — whether the risk is at the app level or the payment processor level.”
The extensive letter points to numerous things Apple already does. From App Store and App Review and beyond, its approach helps control fraud, prevent distribution of pornography, and defend against malware. But, of course, the Commission is actively eroding these protections with the DMA.
Europe is fundamentally undermining itself
“The Commission has forced Apple to change that successful approach — while simultaneously refusing to allow it to implement proven safeguards that have helped ensure that iOS users are better protected from malicious actors than users of any other [approach]. Without those protections, risks to users on our devices will inevitably increase.”
Apple also warns that giving developers permission to link out of their apps to wherever they want to link without any significant protections also threatens user security. Needless to say, this is precisely what Europe has demanded Apple do — a move that will inevitably expose people to additional risks. Europe is also insisting Apple “fundamentally undercut” many of the tools it currently uses for parental protection and control, even to the extent of refusing to permit Apple to institute key safeguards.
“For decades, Apple has been meeting the challenges of an ever-evolving threat landscape by constantly innovating to keep our users safe from harm. Our efforts have made iOS the most secure mobile platform,” the company, quite justifiably, explains.
Apple also points to some of the big companies that have undermined the very protections the Commission now claims to want to encourage.”
European enshittification
“The Commission has made the App Store less safe for users: It introduced new vulnerabilities and undermined the protections Apple has long put in place to protect users of the App Store,” Apple said. “At the same time, the Commission has done nothing to address abuses by developers. Authorities in the United States have condemned Epic Games, Match Group, and other developers for misleading and deceiving users (specifically including children, in at least one case). The silence of the Commission has been deafening. It has turned a blind eye to these abuses, as they would expose the hypocrisy of the Commission’s approach to the digital marketplace. The loser is the user.
“It does not make sense for the Commission to press Apple to protect users, including minors, from fraud within the App Store while at the same time requiring Apple to create functionalities like link-outs and web views that increase the risk of fraud without necessary safeguards.”
Where’s the consistency?
“The Commission cannot both prohibit Apple from taking the steps it has found essential in mitigating the risk of scams and fraud on the App Store while simultaneously scrutinizing Apple for not providing even more measures to mitigate these risks on the App Store.”
Apple is quite evidently in a Catch-22 situation. On one hand, it’s being forced to introduce fundamental insecurities into its platforms, while at the same time facing punishment for what it is required to do. Central to all of this is what appears to be a commitment to denial on the part of Europe, which can’t even accept, for example, that many fraudsters play a long game; that is why intentional use of third-party payment systems with multiple layers of approval is so important when it comes to NFC.
What next?
With that total lack of consistency, Apple will surely see the cost of doing business in Europe increasing fast. So, when will it become so burdensome and expensive to do business in Europe that it becomes worth quitting the market?
This has to be a question Apple’s senior leadership teams must discuss at morning meetings as Europe’s regulators hammer Cupertino with contradictory and inconsistent requests. If European voters feel like the long wait for Apple Intelligence was painful to them, just how will they feel in the event Apple chose to withdraw some products and services from that market entirely?
Perhaps Europe’s Parliament, which hires the leaders of the Commission, might want to consider that in the prelude to the next election in 2029.
You can follow me on social media! Join me on BlueSky, LinkedIn, and Mastodon.
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
M365 Copilot data processing goes local to meet sovereignty demands
Microsoft will allow customers in 15 countries to process Microsoft 365 Copilot data locally, part of the company’s plans to address growing digital sovereignty concerns in regions such as Europe.
Data generated during interactions with the generative AI (genAI) assistant — including user prompts and output responses — will be handled in data centers within each country Microsoft announced Tuesday.
The rollout will begin with Australia, India, Japan, and the United Kingdom by the end of the year, followed by Canada, Germany, Italy, Malaysia, Poland, South Africa, Spain, Sweden, Switzerland, the United Arab Emirates and the United States in 2026.
The aim is to help M365 Copilot customers, particularly those in government and highly regulated industries, meet “governance, security and regulatory compliance demands,” Paul Lorimer, Microsoft corporate vice president, Office 365 Enterprise and Cloud Engineering, said in a blog post Tuesday.
“With in-country processing, Copilot interactions are processed, under normal operations, in data centers located within a nation’s borders, giving customers greater control over their data,” said Lorimer. Local processing can also improve the genAI assistant’s performance by reducing latency, he said.
Amid rising geopolitical tension, customers in some regions want their data — and the processing of that data — confined to “specific regional, if not local, data centers,” said Nader Henein, research vice president analyst at Gartner. “This is meant as an additional level of regulatory protection where data stored locally is governed by local laws and further insulated from extra-territorial reach.”
As demands for data residency have risen, Microsoft introduced its Advanced Data Residency add-on for Microsoft 365 apps, but not Copilot processing, “due to limitations in GPU capacity. Now this has changed, with plans to support local processing in a series of 15 regional data centers,” he said.
“For organizations that had prioritized storage and processing residency as a key requirement, the adoption of Copilot capabilities within the Microsoft stack was delayed — with this change, they have a path to adoption.”
The announcement builds on Microsoft’s earlier efforts to address European data sovereignty concerns, in particular.
Early this year, Microsoft published its European “digital commitments,” promising to “uphold Europe’s digital resilience regardless of geopolitical and trade volatility.” It also introduced services such as Data Guardian, which restricts access to customer data to Microsoft staff residing in Europe, and Microsoft 365 Local, which enables customers to run applications including SharePoint Server and Exchange Server on their own systems with Azure Local.
Microsoft 365 Local is now generally available, the company said, with a disconnected option for “complete isolation” due in early 2026.
Other announcements this week include the establishment of a European board of directors comprising European nationals to oversee data center operations in compliance with European law. Microsoft also extended AI data to its European Union Data Boundary service, meaning European customers’ AI data will be stored and processed exclusively in the EU, “whether at rest or in transit.”
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Office sandbox file security to disappear from enterprise Windows by late 2027, Microsoft confirms
Windows enterprise administrators will have until December 2027 at the latest to put in place alternatives to the security protection offered by Microsoft Defender Application Guard (MDAG) for Office, the company has confirmed.
MDAG’s purpose is to protect customers from the threat of boobytrapped Office documents sent via email. The feature was added to some Office subscription tiers from 2019 onwards, but Microsoft announced in November 2023 that the feature was nearing the end of the road, since when customers have been waiting for more detail on how and when this would happen.
According to Microsoft’s new timeline on its customer portal, removal will begin with Office version 2602 for the Current Patch Tuesday Channel in February 2026, the Monthly Enterprise Channel in April 2026, and the Semi-Annual Enterprise Channel in July 2026.
Full removal will happen for Office version 2612 by December 2026 for the Current Channel, February 2027 for the Monthly Enterprise Channel, and July 2027 for the Semi-Annual Enterprise Channel.
Ambiguously, the timeline also lists December 2027 as the final date for removal, although it’s likely that the later date is a final cut-off for customers with extended support licenses.
Isolation overhead
Instead of opening files in main memory, MDAG opens files in a Hyper-V sandbox, thereby isolating any malware executed from the operating system. The concept is sound, but it comes with the inconvenience of much slower document load times.
It could also be undermined by occasional vulnerabilities in the isolation layer, an example of which would be CVE-2022-26706, a sandbox escape flaw affecting macOS.
Microsoft is replacing MDAG with two security layers it claims do the same job: Attack Surface Reduction (ASR) rules and Windows Defender Application Control (WDAC).
ASR is a rules-based mechanism for blocking malicious scripts, executables, or code injection. While the performance is much improved, one potential downside is that it relies on behavioral analysis.
What happens if attackers use a novel technique not yet picked up by ASR? Microsoft’s view is that they rarely do because most malicious document attacks exploit predictable techniques. Backed by cloud-based machine learning, the chances of an innovative attack getting past ASR are claimed to be small.
Meanwhile, WDAC analysis, which executes at kernel level, blocks applications by monitoring digital signatures, file hashes, and other reputation signals.
Admin workload
Given that the removal process happens automatically, what’s left for administrators to do?
Although many enterprise IT teams are probably not hugely aware of MDAG, there could still be hidden work caused by its removal. Microsoft, for its part, recommends that administrators do the following:
Enable Microsoft Defender for Endpoint ASR rules to block risky Office file behaviors.
Enable Windows Defender Application Control (WDAC) to ensure only trusted, signed code runs on devices.
Review internal documentation and helpdesk guidance if your organization previously relied on Application Guard for Office.
Nevertheless, MDAG’s deprecation could still cause problems for customers that have built it into automated workflows.
A generic example of this would be an automated workflow script that will only allow an Office document to be opened once it has passed through MDAG. If MDAG is no longer present, that script will need to be re-written — and procedures changed if the logs from isolation security testing were being sent into SIEMs as part of compliance rules.
Although primarily affecting organizations with a cautious approach to Office documents such as critical infrastructure or government, this re-scripting could still turn into a lot of work.
What’s not in doubt is the stress induced by the regular churn of new and deprecated features on a Windows platform that has gradually become byzantine in its complexity.
Since 2017, Computerworld has published a regularly updated guide to Windows 10 and 11 components and features as they appear, or disappear. Meanwhile, the arrival of Windows 11 has introduced several changes to the operating system’s underlying security architecture, many built around Security Copilot.
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Forrester: Companies regret many AI-related layoffs
A new report from Forrester suggests that many companies that have been cutting workers in the name of AI are likely to face a backlash, according to The Register.
“Many companies claim they are laying off staff because of AI. Some of these ventures lead to spectacular failures…. Other times, AI doesn’t actually replace human workers at all. Too often, company management lays off employees based on the future promise of AI,” the research firm said.
According to the analysis, 55% of employers now regret laying off staff because of AI. In addition, more decision-makers responsible for AI investments believe the technology will increase the workforce in the coming year, rather than reduce it. “We predict that much of this work will be placed on low-paid workers, either offshore or at lower wages,” Forrester said.
HR functions, in particular, risk being hit hard. Those departments are expected to be dramatically downsized, while still being expected to deliver the same level of service with AI tools.
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
What are ‘Background Security Improvements’ on Apple devices?
Apple has a great reputation for platform security, one it has earned through consistent focus on keeping its operating systems secure.
However, as the number of threats against its platform grows, it needs to find ways to stay ahead. That’s why Apple’s latest iOS, iPadOS, and macOS updates enable a new security feature, Background Security Improvements. What do they mean to you?
What are Background Security Improvements?
Background Security Improvements replace the company’s existing “Rapid Security Response’”feature that provided security patches without needing to offer a full system update.
It means you and your devices should always be protected against dangerous security vulnerabilities as they are identified. That’s good for all of us — and good for IT staffers, who will not need to spend time encouraging people to install vital security patches.
It’s a protective mantle that extends across Apple’s entire ecosystem, which is perhaps yet another reason to switch from the comparatively less secure Windows platform.
What do Background Security Improvements do?
Apple describes this feature as providing, “lightweight security releases for components such as the Safari browser, WebKit framework stack and other system libraries that benefit from smaller, ongoing security patches between software updates.”
The goal is to enable Apple to respond even more swiftly than it does already.
Once it’s enabled:
Patches can install silently in the background without additional interaction.
Apple can remove faulty patches in the event of compatibility problems.
General information concerning security updates will be published on the Apple Support site after each release, along with CVE details, if any.
The protection means users can be certain their Apple devices are as secure as possible. That extends to improved protection against newly identified zero-day attacks, making Apple’s platforms far more resilient.
What you need to think about
The background nature of these security patches is good for most of us most of the time, though some users and certainly some MacOps professionals will want to disable the feature. There are, after all, many enterprises that need to test and approve software patches before they can be installed across their device fleets.
Admins need to ensure their MDM systems can accurately parse data on which updates have been installed across their fleets; hopefully, Declarative Device Management will be (or has already been) updated to provide IT with up-to-date information on this. They will want to be certain all devices have been updated, if company policy is to permit such updates.
It’s worth noting that Apple also patched around 50 vulnerabilities within the same software update that introduced Background Security Improvements. This in itself should be food for thought for Apple users and Apple admins, as it shows the scale of the threat environment and reinforces the need for swift and timely security updates/
Will it work?
It is interesting to think about the tech Background Security Improvements replace, Rapid Security Responses. Those were only used a few times in 2023 and then not used again, so it is possible the company identified a problem in their implementation.
There were reports of problems with the original implementation, including broken websites, installation failures, and exposure to unexpected system messages. Those problems have presumably been rectified with Background Security Improvements. If not, it is reassuring that in case of compatibility problems Apple can remotely remove a problem patch.
Turn it on (or off) again
You can enable this feature in Settings>Privacy & Security>Background Security Improvements, which should be set to Automatically Install.
If you switch the protection off, your device will not receive the security patches until they are included and made available within a subsequent software update.
Stay safe out there!
You can follow me on social media! Join me on BlueSky, LinkedIn, and Mastodon.
Source:: Computer World
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
How Volunteering at TECHSPO Technology Expo Can Jumpstart Your Career
For tech professionals, maintaining a competitive edge is imperative. Participating in industry events emerges as a strategic approach to networking and staying abreast of technological advancements. The TECHSPO Technology Expo, an integral component of the esteemed DigiMarCon conference series, exemplifies this opportunity.
Contributing to TECHSPO affords you the chance to interact with industry luminaries, acquire knowledge on emerging technologies, and broaden your professional network. This engagement can significantly propel your career, providing invaluable hands-on experience and forging critical connections.
Discovering new opportunities is the core mission of TECHSPO . As a cornerstone of DigiMarCon, it serves as a unique conduit for professional development.
What Makes TECHSPO Technology Expo a Career Catalyst
TECHSPO Technology Expo has emerged as a preeminent event within the tech sphere, drawing professionals from every corner of the globe. As a cornerstone of a global conference series, it offers a distinctive amalgamation of innovation, networking, and educational opportunities. These elements collectively serve to significantly elevate a tech professional’s career trajectory.
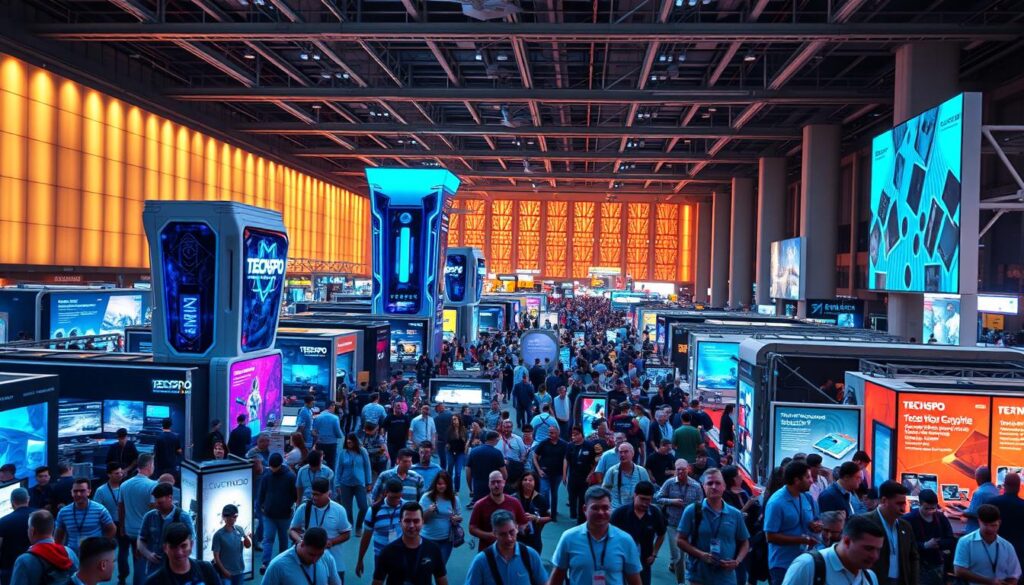
As a global event with a diverse attendee base, TECHSPO Technology Expo serves as a nexus where tech aficionados can engage with industry stalwarts, explore cutting-edge technologies, and uncover novel career avenues. Its global influence and accessibility render it an exemplary venue for networking and knowledge acquisition.
The Global Impact and Reach of TECHSPO
TECHSPO Technology Expo transcends the confines of a local gathering, being an integral part of a global conference series that spans multiple cities worldwide. This international footprint ensures a diverse assembly of attendees, encompassing industry veterans and tech aficionados alike. A tech industry luminary opined, “Global tech events like TECHSPO are indispensable for cultivating innovation and cross-border collaboration.”
“The global scope of TECHSPO facilitates a rich exchange of ideas and technologies, positioning it as a prime destination for tech professionals seeking to broaden their vistas.”
The global dimension of TECHSPO also affords attendees a broad spectrum of perspectives and insights, rendering it an invaluable experience for those aspiring to ascend in the tech domain.
Why Tech Professionals Flock to This Premier Event
Tech professionals are attracted to TECHSPO Technology Expo for several compelling reasons. Firstly, the event provides unparalleled networking opportunities with industry luminaries and peers. Secondly, it grants access to the most recent technological advancements and trends, enabling attendees to remain at the forefront of the industry. Lastly, volunteering at TECHSPO can be a strategic career advancement move, affording hands-on experience and invaluable connections.
- Networking opportunities with industry leaders
- Access to the latest technologies and trends
- Hands-on experience through volunteering
- Valuable connections for career advancement
By participating in and volunteering at TECHSPO Technology Expo, tech professionals gain entry into a global community that is propelling innovation and transformation within the tech sector.
Volunteering at TECHSPO Technology Expo: A Gateway to Opportunity
Engagement in TECHSPO ‘s volunteer program opens a portal to a multitude of opportunities, significantly bolstering one’s career trajectory. This endeavor not only affords participation in a vibrant event but also serves as a conduit for interaction with industry stalwarts, innovators, and peers of similar professional inclinations.

Building Your Professional Network Through Volunteer Engagement
Participation in TECHSPO Technology Expo facilitates the construction of a substantial professional network. Through interactions with attendees, presenters, and fellow volunteers, one cultivates relationships that may evolve into collaborative ventures or career advancement opportunities.
The expo’s extensive array of activities and sessions offers numerous avenues for networking with professionals from diverse tech industry segments. Whether your interests lie in software development, AI, or cybersecurity, you will encounter individuals with similar professional aspirations.
Gaining Insider Access to Cutting-Edge Technologies
One of the primary advantages of volunteering at TECHSPO is the opportunity to gain direct access to the most advanced technologies and innovations. As a volunteer, you will have the privilege of exploring exhibition stands, attending workshops, and participating in product unveilings, affording you a unique glimpse into the future of technology.
This exposure is invaluable for maintaining a competitive edge in your career, whether you seek to acquire new competencies or remain abreast of the latest industry developments.
Developing Soft Skills That Employers Covet
Volunteering at TECHSPO also enables the acquisition of critical soft skills that employers highly esteem. Skills such as communication, teamwork, problem-solving, and adaptability are refined through practical application in a real-world context.
By assuming diverse roles and working under the mentorship of seasoned professionals, you will have the opportunity to showcase your capabilities and compile a portfolio of skills that can be presented to prospective employers.
Available Volunteer Roles and Responsibilities at TECHSPO
TECHSPO Technology Expo presents a plethora of volunteer opportunities for individuals aspiring to immerse themselves in the tech sector. This encompasses a broad spectrum, from students and professionals in transition to tech enthusiasts. Each category finds a suitable role within the event’s framework.
Registration and Check-In Team Positions
The registration and check-in team serves as the initial interface for attendees, rendering it indispensable to the TECHSPO experience. Volunteers in this capacity are entrusted with overseeing the registration desk, addressing attendee inquiries, and facilitating a seamless check-in process.
Key responsibilities encompass:
- Assisting attendees with registration and check-in
- Providing information about the event schedule and layout
- Resolving any issues that may arise during the check-in process
Technical Support and AV Assistance Roles
TECHSPO ‘s operational success hinges on its technological infrastructure. Volunteers with technical acumen are indispensable in ensuring the event’s smooth execution.
Responsibilities include:
- Setting up and testing audiovisual equipment
- Troubleshooting technical issues during presentations and demonstrations
- Assisting speakers and presenters with their technical needs
Speaker and VIP Liaison Opportunities
As a speaker or VIP liaison, you’ll engage with industry luminaries and innovators. Your role entails ensuring that speakers and VIP guests receive requisite support during their tenure at TECHSPO .
Key duties include:
- Coordinating with speakers and VIP guests to understand their needs
- Assisting with speaker introductions and ensuring they have the necessary materials
- Providing VIP guests with personalized support and information
Social Media and Content Creation Volunteers
TECHSPO offers opportunities for those with a penchant for social media or content creation to contribute to event promotion and online engagement.
Responsibilities may include:
- Creating and scheduling social media posts to promote the event
- Capturing content during the expo to share on social media channels
- Engaging with attendees online to build a community around TECHSPO
Volunteering at TECHSPO not only contributes to the event’s success but also affords invaluable experience and industry connections. Whether your interest lies in technical support, registration, or social media management, TECHSPO offers a volunteer role tailored to your aspirations.
How to Apply and Secure a Volunteer Position at TECHSPO
The initiation of volunteering at TECHSPO necessitates a comprehension of the application and selection methodologies. To attain a volunteer position, it is imperative to be cognizant of the fundamental steps and the associated timelines.
Application Timeline and Important Deadlines
The volunteer application process for TECHSPO typically commences several months prior to the event. It is imperative to consult the official TECHSPO website for the precise application timeline and important deadlines. Noting these dates in your calendar will prevent the omission of the application opportunity.
To provide an initial framework, the following is a general outline:
- Application opens: 4-6 months before the event
- Application closes: 6-8 weeks before the event
- Interviews conducted: 4-6 weeks before the event
- Selection notifications sent: 2-4 weeks before the event
Creating a Standout Volunteer Application
When applying to volunteer at TECHSPO , your application must emphasize your pertinent skills and experiences. Customize your application to the specific role you aspire to, illustrating the congruence of your skills with the event’s requirements.
A distinguished application encompasses:
- A succinct and clear personal statement detailing your motivation for volunteering
- Relevant experience or skills directly applicable to the volunteer position
- Professional references or recommendations, if necessitated
Interview Process and Selection Criteria
Upon successful application, you will be invited to an interview as part of the selection process. This phase serves as an opportunity for the TECHSPO team to evaluate your aptitude for the volunteer role and for you to garner insights into the event.
To excel in the interview, prepare to discuss your:
- Motivation for volunteering at TECHSPO
- Relevant skills and experiences
- Capacity to function as a team member and adapt to a dynamic environment
By grasping the application timeline, crafting an impactful application, and excelling in the interview, your prospects of securing a volunteer position at TECHSPO will be significantly augmented.
Preparing for Your TECHSPO Volunteer Experience
Embarking on the journey of volunteering at TECHSPO necessitates the cultivation of specific competencies, a thorough comprehension of the event’s spatial arrangement, and a readiness for the assigned responsibilities. This preparatory phase is instrumental in guaranteeing a fruitful and gratifying experience, positioning you advantageously for future engagements within the tech sector.
Essential Skills to Develop Before the Event
To maximize the value of your volunteer engagement at the techspo expo, it is imperative to hone relevant skills prior to the event. Key competencies include:
- Communication and teamwork skills
- Technical skills pertinent to your designated role
- Problem-solving and adaptability
Acquiring these skills will empower you to adeptly manage the event’s demands, leaving a lasting positive impression on both attendees and organizers.
Understanding the TECHSPO Schedule and Layout
Acquaintance with the TECHSPO schedule and layout is critical for achieving volunteer success. This entails grasping the event’s timeline, identifying the locations of critical areas such as registration, exhibition halls, and speaker rooms, and being cognizant of any specific regulations or protocols.
By mastering the layout and schedule, you will navigate the event seamlessly, ensuring timely presence in key locations, and delivering optimal support to attendees and exhibitors.
Packing and Preparation Tips for Volunteers
To guarantee your readiness for the TECHSPO volunteer role, it is vital to assemble the appropriate items and prepare adequately for the event. Some preparatory measures include:
- Donning comfortable attire and footwear
- Carrying essentials such as water, snacks, and a portable charger
- Retaining a copy of your schedule and contact details for the organizing team
Through meticulous preparation, you will be able to concentrate on delivering an outstanding experience for attendees, maximizing your time at the event.
Maximizing Networking Opportunities While Volunteering
Engagement in TECHSPO ‘s volunteer program places you at the epicenter of the tech sector, amidst a plethora of collaborators and employers. This vantage point empowers you to harness techspo expo volunteer opportunities for professional progression.
As a volunteer, you gain access to a broad spectrum of professionals, encompassing industry stalwarts and prospective employers. To fully capitalize on these volunteer benefits at techspo expo, a strategic mindset is imperative.
Strategic Networking: Who to Connect With and How
Effective networking at TECHSPO necessitates the identification of key individuals and groups for connection. Consider the following strategies:
- Research speakers and attendees beforehand to pinpoint prospective contacts.
- Opt for volunteer roles that facilitate direct interaction with industry professionals, such as registration or speaker liaison positions.
- Engage in conversations during the event, posing insightful questions to initiate profound discussions.
Crafting Your Perfect Elevator Pitch for TECHSPO
A meticulously crafted elevator pitch is vital for leaving a lasting impression at TECHSPO . Your pitch should succinctly articulate your professional identity, spotlighting your competencies and interests. Here are some guidelines:
- Initiate with a compelling opening that captures attention.
- Explicitly articulate your professional background and objectives.
- Conclude with a call to action, such as exchanging contact details.
Following Up with Contacts After the Event
The networking endeavor does not conclude with TECHSPO ‘s conclusion. The act of following up with your new contacts is indispensable for cultivating enduring relationships. Consider the following:
- Dispatch a personalized email or LinkedIn message within a week of the event.
- Refer to specific conversations or shared interests to re-establish context.
- Propose a follow-up meeting or call to further explore collaborative possibilities.
By adopting these strategies, you can transform your tech conference volunteer opportunities into significant connections, driving your career advancement.
Turning Your TECHSPO Volunteer Experience into Career Advancement
The experience and connections derived from volunteering at TECHSPO can serve as a catalyst for career progression. As a volunteer, you integrate into a distinguished event, drawing in tech professionals and industry leaders globally.
Adding TECHSPO to Your Resume and LinkedIn Profile
Emphasizing your TECHSPO volunteer experience on your resume and LinkedIn profile can significantly enhance your visibility to prospective employers. It showcases your proactive stance towards career development and your engagement with the tech community.
When incorporating TECHSPO into your resume, ensure to:
- Detail your role and responsibilities as a volunteer
- Highlight any skills you developed or utilized during the event
- Quantify your achievements, such as the number of attendees you interacted with or the success of the events you helped organize
Leveraging Your Experience in Job Interviews
Your TECHSPO volunteer experience can be a valuable asset in job interviews. It demonstrates your capability to thrive in a fast-paced environment, manage multiple tasks, and interact with diverse groups.
To effectively leverage this experience:
- Prepare examples of your accomplishments and challenges faced during TECHSPO
- Emphasize the skills you developed that are relevant to the job you’re applying for
- Discuss how your experience at TECHSPO has prepared you for the role and how you can contribute to the organization
Using TECHSPO Connections for Job Referrals
The connections forged at TECHSPO can be a powerful resource for job referrals. Networking with industry professionals, speakers, and other volunteers can lead to valuable recommendations and insider information about job openings.
To maximize the value of your TECHSPO connections:
- Follow up with new contacts after the event to maintain relationships
- Engage with TECHSPO alumni on professional networking platforms
- Leverage these connections to get referrals or advice on job opportunities
Continuing Education Opportunities Discovered at TECHSPO
TECHSPO is not merely an event; it is a gateway to discovering continuing education opportunities. From workshops to keynote speeches, attendees are exposed to the latest trends and technologies in the tech industry.
To continue your education:
- Take note of the sessions and workshops that interest you the most
- Research the presenters and their organizations for possible collaboration or learning opportunities
- Utilize the connections you made to inquire about additional training or certification programs
Success Stories: How TECHSPO Volunteering Launched Careers
The TECHSPO Technology Expo has emerged as a transformative platform for tech enthusiasts and professionals, serving as a catalyst for successful tech careers. It offers a unique opportunity to engage with the latest technological advancements, foster professional networks, and acquire invaluable experience through its volunteer program.
From Volunteer to Tech Industry Leader
Transitioning from volunteer to tech industry leader is a narrative echoed by several individuals. Their journeys underscore the profound impact of volunteering at TECHSPO , highlighting the career growth and experiential value derived from such endeavors. Notably, some have secured full-time roles at premier tech companies, leveraging their dedication and skills showcased during the event.
Key takeaways from their experiences include:
- Developing a strong network of contacts within the industry
- Gaining insights into the latest technological advancements
- Enhancing soft skills such as communication and teamwork
Landing Dream Jobs Through TECHSPO Connections
TECHSPO has been instrumental in facilitating the acquisition of dream jobs for numerous attendees. It serves as a nexus for talent and opportunity, enabling volunteers to demonstrate their technological prowess and passion. By participating in the TECHSPO expo’s volunteer program, individuals significantly enhance their visibility to leading tech companies.
The event’s connections have resulted in job offers, internships, and collaborative projects on innovative ventures. TECHSPO ‘s volunteer program is meticulously designed to cultivate these connections, providing a conduit for aspiring professionals to engage with industry stalwarts.
Entrepreneurial Success Stories Born at TECHSPO
TECHSPO has been the incubator for several entrepreneurial ventures. Volunteers have been inspired by the technologies and trends presented at the expo, leading to the inception of innovative startups. The insights and experience garnered during volunteering have been critical in shaping these entrepreneurial endeavors.
“TECHSPO was the catalyst for our startup. The connections we made and the technologies we were exposed to during our volunteering experience were instrumental in our journey.”
Career Pivots Inspired by TECHSPO Experiences
For some, volunteering at TECHSPO has been a transformative experience, prompting a career pivot into the tech industry. The hands-on experience and exposure to cutting-edge technologies have motivated many to transition into new roles or industries, leveraging the skills and confidence gained during their time at TECHSPO .
By becoming a volunteer at TECHSPO expo, individuals not only contribute to the event’s success but also open themselves up to a plethora of opportunities in the tech sector. The tech volunteer positions at TECHSPO expo offer a unique vantage point at the forefront of technological innovation.
Conclusion: Taking the First Step Toward Your Tech Career Breakthrough
Engagement in TECHSPO Technology Expo’s volunteer initiatives represents a strategic pivot for aspirants in the tech sector. Such involvement affords direct exposure to industry practices, facilitates the expansion of professional networks, and provides a vantage point for understanding current technological advancements.
The array of advantages derived from volunteering at TECHSPO is extensive, encompassing the refinement of soft skills and access to state-of-the-art technologies. As a volunteer, one becomes a critical component of the event’s triumph, collaborating with industry stalwarts and innovators.
To fully capitalize on the volunteer opportunities at techspo expo, initiating the application process is imperative. This action not only contributes to the success of a leading tech event but also propels personal career advancement. Do not overlook this opportunity to enhance your professional trajectory – submit your application to volunteer at TECHSPO and embark on a transformative journey in your tech career.
FAQ
What is TECHSPO Technology Expo, and how can volunteering there benefit my career?
TECHSPO Technology Expo, a cornerstone of the DigiMarCon conference series, serves as a nexus for industry luminaries, a crucible for technological innovation, and a fertile ground for professional networking. Volunteering at this event affords you direct exposure to cutting-edge technologies, invaluable connections, and potentially, a springboard to new career vistas.
What kind of volunteer roles are available at TECHSPO Technology Expo?
TECHSPO proffers a diverse array of volunteer positions, ranging from registration and check-in to technical support and social media management, accommodating a broad spectrum of skills and interests.
How do I apply to volunteer at TECHSPO Technology Expo?
To secure a volunteer position, it is imperative to navigate the application process adeptly. This entails a thorough understanding of the application timeline, the creation of a compelling application, and the acing of the interview process.
How can I make the most of my TECHSPO volunteer experience?
To optimize your volunteer experience, it is advisable to hone essential skills, grasp the event’s schedule, and prepare thoroughly. Such preparation ensures a seamless and productive experience, facilitating the maximization of networking opportunities.
Can volunteering at TECHSPO really help me advance my career?
Absolutely, your volunteer experience at TECHSPO can significantly bolster your career trajectory. It is advisable to showcase this experience on your resume and LinkedIn profile, leverage it during job interviews, and utilize your connections for job referrals. This translation of volunteer experience into tangible career benefits can be transformative.
What are some tips for maximizing networking opportunities while volunteering at TECHSPO ?
To maximize networking opportunities, it is strategic to identify key contacts, craft a persuasive elevator pitch, and follow up with these contacts post-event. This approach can significantly enhance your networking efficacy, potentially opening doors to new career prospects.
Are there any success stories of individuals who have volunteered at TECHSPO and gone on to achieve career success?
Yes, numerous success stories attest to the career-launching and career-advancing capabilities of TECHSPO . These narratives detail individuals’ ascension to tech industry leadership and attainment of dream jobs, underscoring the profound impact of the connections and experiences garnered through TECHSPO volunteering.
How can I continue my education and professional development after volunteering at TECHSPO ?
TECHSPO offers a plethora of continuing education opportunities. Leveraging your experience and connections can facilitate further learning and professional advancement.
What is the global impact of TECHSPO Technology Expo, and how can volunteering contribute to my global professional network?
As part of a global conference series, TECHSPO attracts tech professionals from around the world. Volunteering at TECHSPO allows you to tap into this global community, potentially broadening your career prospects and expanding your professional network on a global scale.
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026
Behind the Scenes: What It’s Like to Volunteer at TECHSPO Technology Expo
Envision yourself immersed in an event that epitomizes technological advancement and innovation. As a volunteer at TECHSPO Technology Expo, a cornerstone of the DigiMarCon Conferences, you will occupy a central position. This role affords you the chance to engage with industry elites, stay abreast of emerging trends, and acquire practical experience.
Volunteering at TECHSPO offers a distinctive experience, enriching your understanding while enabling you to contribute to the tech sphere. With a variety of roles available, you can select the one that aligns with your interests, whether it involves assisting with setup, handling registrations, or supporting the technical teams.
By participating in TECHSPO , you become an integral part of a dynamic community that is redefining the technological landscape. This is your opportunity to be a part of a leading tech event and contribute meaningfully to its success.
The TECHSPO Experience: America’s Premier Tech Expo
TECHSPO , as America’s vanguard tech expo, amalgamates the crème de la crème of the industry, innovators, and aficionados, spotlighting the most advanced technological breakthroughs. It is convened in the most elite 5-star venues across the United States, underscoring its status as a cornerstone of the DigiMarCon Conferences, renowned for their caliber of events.
What Makes TECHSPO Stand Out in the Tech Conference Landscape
TECHSPO distinguishes itself through its exhaustive exploration of the tech sector, encompassing a myriad of subjects from avant-garde technologies to pioneering business paradigms. The event’s capacity to amalgamate a diverse array of stakeholders, including industry titans, nascent ventures, and academic entities, fosters a singular milieu conducive to networking and synergistic collaboration.
The expo’s dedication to illustrating the practical deployment of nascent technologies renders it an indispensable resource for professionals aspiring to integrate the most current trends into their professional endeavors.
The Scale and Scope of TECHSPO Events Across the United States
TECHSPO ‘s events are staged in the country’s major metropolises, ensuring that the tech community’s engagement is accessible to a broad demographic. The magnitude of these gatherings is considerable, with thousands of attendees and hundreds of exhibitors participating in each expo.

The events span a wide array of technologies, including AI, cybersecurity, blockchain, and others, providing a holistic perspective on the contemporary tech milieu.
Key Technologies and Innovations Showcased at Recent Events
Recent TECHSPO gatherings have underscored several critical technologies, such as AI, IoT, and quantum computing advancements. These innovations are presented through exhibitions, demonstrations, and conference sessions, affording attendees an in-depth exploration of the latest advancements.
The focus on practical applications and real-world exemplars enables attendees to grasp the transformative influence these technologies could exert on their respective sectors.
What It’s Like to Volunteer at TECHSPO : A First-Hand Account
Engaging in volunteer work at TECHSPO transcends the ordinary, merging technological advancements, innovative spirit, and communal engagement. Volunteers, integral to the event’s success, derive profound experiences while contributing to its vibrancy.

A Day in the Life of a TECHSPO Volunteer
The daily activities of a TECHSPO volunteer encompass a diverse array of tasks and responsibilities. From the meticulous setup of exhibition booths to the provision of technical support to both speakers and attendees, volunteers are indispensable to the event’s seamless execution.
- Assisting with registration and check-in processes
- Providing technical support to exhibitors and speakers
- Helping to manage the flow of attendees throughout the venue
Volunteers frequently express the exhilaration and dynamism that pervades the event. The TECHSPO experience is crafted to be both engaging and unforgettable, with numerous networking opportunities and encounters with industry luminaries, akin to those found at DigiMarCon.
The Excitement and Energy Behind the Scenes
Behind the scenes, volunteers are the pulsating core of the event. Their fervor and commitment imbue the atmosphere with an electric charge, felt by all attendees. Whether addressing technical challenges or serving as a welcoming presence in a bustling environment, volunteers significantly impact the event’s success.
The TECHSPO volunteer community is renowned for its camaraderie and collaborative spirit.
Through shared experiences and a collective sense of purpose, volunteers forge enduring connections with their peers, united by their contributions to a significant endeavor.
Balancing Responsibilities and Enjoying the Experience
Though the duties of volunteering at TECHSPO are considerable, participants are encouraged to savor the experience. Access to keynote addresses, workshops, and exhibitions ensures a wealth of opportunities for learning and personal growth.
- Engage in networking activities to forge connections with industry pioneers and innovators.
- Explore the diverse exhibitions and demonstrations available.
- Participate in workshops and sessions to enhance your knowledge and skills.
By harmonizing their volunteer obligations with personal interests, TECHSPO volunteers can optimize their experience, fully benefiting from their time at the event.
Types of Volunteer Roles and Responsibilities
TECHSPO presents a spectrum of volunteer positions, tailored to diverse skill sets and interests. These volunteers are indispensable to the TECHSPO Technology Expo, ensuring its seamless operation. Their contributions span from registration to technical support, crafting an unforgettable experience for all attendees.
Registration and Check-in Teams: Creating the First Impression
The registration and check-in teams serve as the initial interface for attendees. Volunteers in this capacity are tasked with welcoming guests, distributing event materials, and disseminating pertinent information. Their approachability and efficiency establish the foundation for a favorable event experience.
- Manage registration desks
- Assist attendees with check-in
- Provide event information and materials
Speaker and VIP Support: Working with Industry Leaders
Supporting speakers and VIPs is a critical function, ensuring their needs are met. This encompasses coordinating with these individuals, fulfilling special requests, and delivering technical support during their presentations.
- Coordinate with speakers and VIPs
- Arrange for special requests
- Provide technical support during presentations
Technical Assistance and Setup Crews: Ensuring Smooth Operations
The technical assistance and setup crews are instrumental in the event’s behind-the-scenes functionality. Their duties include setting up exhibit booths, testing audiovisual equipment, and resolving technical issues.
- Set up exhibit booths and equipment
- Test audiovisual equipment
- Troubleshoot technical issues during the event
Social Media and Content Creation Teams: Sharing the TECHSPO Story
Volunteers on the social media and content creation teams are responsible for amplifying the TECHSPO narrative. They document the event’s vibrancy through photographs, videos, and compelling content.
- Create engaging content for social media
- Capture photos and videos of the event
- Share attendee experiences and feedback
Engagement in these roles not only bolsters TECHSPO ‘s success but also affords volunteers invaluable industry experience and networking opportunities.
The Application Process: How to Become a TECHSPO Volunteer
Initiating the journey towards volunteering at TECHSPO necessitates a thorough comprehension of the application process, a rigorous endeavor. This endeavor not only affords the privilege of participating in a distinguished tech exposition but also presents an avenue for networking with industry elites and acquiring invaluable experience.
Application Timeline and Deadlines for Major TECHSPO Events
The timeline for applying for TECHSPO volunteer positions is typically disclosed concurrently with the event’s dates. It is imperative to submit applications promptly, as vacancies are swiftly occupied. Early submissions are often prioritized, mirroring the discounts offered by DigiMarCon Conferences for early registrants.
For significant TECHSPO events, the application window typically opens 2-3 months prior to the event. Prospective volunteers are urged to monitor the TECHSPO website for updates on application cutoffs.
Required Qualifications and Experience Levels
The prerequisites for volunteer roles at TECHSPO may differ, yet a common denominator is a fervent interest in technology coupled with adept communication abilities. Certain positions might necessitate specialized technical acumen or prior experience.
- Roles in registration and check-in necessitate proficiency in organization.
- Positions supporting speakers and VIPs benefit from backgrounds in customer service or hospitality.
- Teams responsible for technical assistance and setup require individuals with technical expertise or experience.
Selection Criteria and What TECHSPO Coordinators Look For
TECHSPO coordinators seek volunteers who embody not only expertise but also fervor and dependability. The selection process entails a meticulous review of applications against the criteria for each volunteer position.
“The right volunteers are instrumental in the success of an event. We prioritize individuals who are eager to learn, adept at teamwork, and maintain a positive disposition.” – TECHSPO Volunteer Coordinator
Tips for Standing Out in Your Volunteer Application
To enhance your prospects of selection, it is critical to differentiate your application. Here are some strategies:
- Accentuate any pertinent experience or abilities you possess.
- Express your passion for the tech sector and volunteering.
- Ensure your application is exhaustive and submitted within the stipulated timeframe.
By adhering to these recommendations and comprehending the application process, you can successfully become a TECHSPO volunteer and reap the rewards associated with it.
Training and Preparation for TECHSPO Volunteers
TECHSPO ‘s dedication to excellence is evident in its extensive volunteer training regimen. Recognizing the importance of well-prepared volunteers, the organization commits substantial resources to equip them with the requisite skills and knowledge. This investment is critical for the successful execution of its events.
Pre-Event Orientation Sessions and Materials
TECHSPO initiates thorough pre-event orientation sessions for its volunteers. These sessions aim to acquaint volunteers with the event’s layout, their specific roles, and the event’s overarching objectives. Volunteers are provided with detailed guides and FAQs to aid in their preparation.
The orientation sessions are interactive, mirroring the collaborative learning and audience participation found at DigiMarCon. This includes interactive question and answer sessions. Such an approach ensures volunteers are not only informed but also engaged and motivated.
Essential Skills Development for Different Volunteer Roles
TECHSPO acknowledges the varied skill requirements for different volunteer roles. It offers specialized training for these positions. For example, volunteers at the registration desk receive training on efficient attendee check-in management, while those handling technical aspects learn to troubleshoot common issues.
This targeted training enables volunteers to perform their duties with confidence and effectiveness. It contributes to the event’s overall success. Volunteers also gain valuable experience, beneficial for their future careers in the tech industry.
Team Building Activities and Getting to Know Fellow Volunteers
TECHSPO incorporates team-building activities into its volunteer training program. These activities aim to foster camaraderie among volunteers, facilitating their ability to work together effectively. By cultivating a strong team dynamic, TECHSPO ensures volunteers can support each other during the event, enriching the experience for attendees.
The extensive training and preparation provided by TECHSPO significantly enhance the volunteer experience and contribute to the success of its events. By investing in its volunteers, TECHSPO demonstrates its commitment to delivering high-quality experiences for both volunteers and attendees.
Networking Opportunities for Volunteers
Engagement in TECHSPO Technology Expo as a volunteer presents a singular opportunity to forge connections with the vanguard of the tech sector. In this capacity, you will be an indispensable component of the event, collaborating intimately with exhibitors, speakers, and attendees. This role affords a privileged glimpse into the inner workings of the tech industry, concurrently opening avenues for substantial networking prospects.
Connecting with Industry Leaders and Innovators
TECHSPO ‘s allure lies in its ability to draw a broad spectrum of professionals, encompassing both stalwarts in the industry and nascent startups. As a volunteer, you will have the privilege of engaging with these individuals, garnering insights into their endeavors and reciprocating with your own narratives. This direct interface with industry luminaries can be transformative for your professional trajectory, imparting invaluable knowledge and potentially catalyzing new avenues for advancement.
The event’s architecture is predicated on fostering connections, with numerous interludes and networking forums dispersed throughout the day. Volunteers are implored to engage actively in these forums, augmenting their professional network and cultivating relationships that transcend the event’s duration.
Building Relationships with Fellow Tech Enthuasiasts
Participation in TECHSPO also entails integration into a collective of individuals united by a shared enthusiasm for technology. You will collaborate with fellow volunteers, many of whom are also entrenched in the tech domain. This camaraderie can precipitate enduring professional affiliations and a heightened sense of belonging within the tech fraternity.
Further, the shared endeavor of contributing to the event’s success cultivates a bond amongst volunteers. This collective endeavor fosters an environment conducive to the forging of meaningful connections and the establishment of friendships.
How Past Volunteers Have Leveraged TECHSPO Connections for Career Growth
Previous TECHSPO volunteers have capitalized on the connections forged during the event to propel their professional trajectories. From securing interviews to identifying mentors, the networking opportunities at TECHSPO have been deemed invaluable. By cultivating a professional network at TECHSPO , volunteers can access novel career avenues and prospects.
For example, some volunteers have reported that their interactions with industry luminaries at TECHSPO facilitated internships or job offers. Others have sustained the relationships they forged, continuing to exchange ideas and collaborate on ventures.
Professional Development Benefits of Volunteering at TECHSPO
Engagement in the TECHSPO volunteer program is transformative for those aspiring to ascend in the tech sector. It affords a plethora of advantages, significantly augmenting one’s professional standing and career trajectory.
Resume-Boosting Experience in the Tech Industry
Participation in TECHSPO equips individuals with hands-on experience in orchestrating and executing extensive tech events. This experience is quintessential for anyone desiring to leave an indelible mark in the tech domain. By integrating into the TECHSPO ensemble, volunteers demonstrate their proficiency in navigating expedited environments, managing diverse responsibilities, and synergizing with industry stalwarts.
Skill Acquisition in a Fast-Paced Environment
The TECHSPO volunteer initiative is crafted to pose challenges and facilitate the acquisition of new competencies. Volunteers are immersed in various facets of the tech realm, from event coordination to technical assistance, fostering a diverse skill set. This skill development is imperative in the contemporary employment landscape, where adaptability and a wide-ranging skill repertoire are highly esteemed.
Learning About Cutting-Edge Technologies Firsthand
TECHSPO serves as a platform for unveiling the most advanced technologies and innovations, affording volunteers direct exposure to cutting-edge tech. Through participation, volunteers engage with exhibitors, partake in workshops, and acquire insights into the most current trends and technologies. This direct exposure is invaluable for anyone seeking to remain at the forefront of the tech industry.
Certificate of Participation and Reference Opportunities
Upon the culmination of their volunteer engagement, participants are awarded a Certificate of Participation, a valuable asset for their professional portfolio. TECHSPO coordinators and industry luminaries also extend reference opportunities, further augmenting a volunteer’s professional standing. These prospects can substantially elevate a volunteer’s career trajectory, unlocking new avenues within the tech industry.
Volunteer Perks and Exclusive Access
Engaging as a TECHSPO volunteer affords you a plethora of exclusive advantages, significantly enriching your participation. This role transcends mere volunteerism, presenting a gateway to a myriad of captivating experiences and opportunities. These elements collectively contribute to a profoundly rewarding engagement.
Behind-the-Scenes Access to Exhibits and Demonstrations
One of the most captivating benefits of volunteering at TECHSPO is the exclusive access to exhibits and demonstrations. You will have the privilege of witnessing the latest technological advancements and innovations firsthand, often preceding their public unveiling. This privileged access facilitates direct interaction with exhibitors, fostering opportunities for in-depth questioning and hands-on engagement with state-of-the-art technologies.
Complimentary Attendance to Select Sessions and Workshops
Volunteers are granted complimentary access to select sessions and workshops, significantly broadening their knowledge base. This privilege allows for immersion in industry insights and trends, facilitated by interactions with leading professionals. Many volunteers have underscored the value of these sessions, highlighting their role in expanding professional networks and acquiring critical knowledge.
“The access to sessions and workshops was incredible. I learned so much and met some amazing people in my field.”
TECHSPO Swag and Recognition Programs
TECHSPO volunteers are celebrated through various swag and recognition programs, acknowledging their invaluable contributions. This recognition extends beyond mere appreciation, fostering a sense of belonging within the TECHSPO community. Volunteers receive exclusive merchandise and are formally acknowledged through our recognition initiatives.
- Exclusive TECHSPO merchandise
- Recognition on the TECHSPO website
- Special badges or certificates of appreciation
Post-Event Volunteer Appreciation Activities and Networking
Following the event, TECHSPO organizes a series of appreciation activities to express gratitude to our volunteers. These activities include networking opportunities, facilitating connections among volunteers, speakers, and industry professionals. DigiMarCon exemplifies this with premium meeting spaces and exceptional customer service, facilitating the cultivation of meaningful relationships.
Post-event activities encompass:
- Volunteer appreciation parties
- Networking mixers
- Follow-up webinars or online meetups
By volunteering at TECHSPO , you not only contribute to the event’s success but also accumulate invaluable experiences and connections. These assets can significantly enhance your professional and personal development.
Challenges and Rewards: The Complete TECHSPO Volunteer Experience
Engagement in TECHSPO volunteering transcends mere participation, embodying a complex interplay of hurdles and triumphs. As a volunteer, one’s role is critical to the event’s success, yet it is fraught with obstacles. A thorough comprehension of these elements is essential for prospective volunteers, enabling them to adequately prepare for their assignments.
Common Challenges Volunteers Face and How to Overcome Them
Volunteers at TECHSPO frequently encounter obstacles such as managing large crowds, adapting to last-minute changes, and sustaining their energy throughout the event. TECHSPO addresses these challenges through extensive training, arming volunteers with the requisite competencies to navigate diverse scenarios. Effective communication and teamwork are underscored, aiming to facilitate seamless operations.
During the COVID-19 pandemic, TECHSPO introduced safety protocols like social distancing and enhanced hygiene measures, ensuring a secure environment for volunteers and attendees alike. This adaptability reflects the event’s dedication to safeguarding the well-being of its participants.
Managing Time Between Volunteer Duties and Personal Interests
Integrating volunteer commitments with personal pursuits poses a significant challenge. Volunteers must navigate their time between their TECHSPO responsibilities and other obligations. Effective time management involves prioritizing tasks, setting achievable goals, and utilizing downtime to relax or engage in networking activities.
The Most Rewarding Aspects According to Veteran Volunteers
Experienced TECHSPO volunteers frequently emphasize the sense of community and camaraderie as the most rewarding facets of their involvement. They also value the opportunity to engage with technological advancements, interact with industry elites, and contribute to a vibrant, dynamic environment.
“Volunteering at TECHSPO has been a game-changer for me. Not only have I met incredible people, but I’ve also gained invaluable experience in the tech industry.”
Unexpected Benefits That Make the Experience Worthwhile
Volunteering at TECHSPO can yield unforeseen advantages, such as career progression, professional networking, and a deeper tech industry insight. Many volunteers have reported that their TECHSPO experience has facilitated new career opportunities or bolstered their professional standing.
In summary, while volunteering at TECHSPO presents its challenges, the rewards and benefits significantly outweigh these obstacles. With the appropriate mindset and preparation, volunteers can partake in a rewarding and enriching experience.
Conclusion: Why Volunteering at TECHSPO Is Worth Your Time
Engagement in the TECHSPO volunteer program, an integral component of the DigiMarCon Conferences, presents a distinctive amalgamation of personal and professional enrichment. This endeavor affords participants direct immersion within the tech sector, facilitating interactions with visionary innovators and leaders. It also cultivates essential competencies.
The advantages of volunteering at TECHSPO are diverse, encompassing enhancements to one’s professional portfolio and privileged access to avant-garde technologies. This experience offers unparalleled insights into the inner workings of tech conferences. Recognizing the value of volunteering at TECHSPO is imperative; it represents an opportunity to contribute to America’s foremost tech exposition, concurrently propelling one’s career trajectory.
Insights into the TECHSPO volunteer program unveil a profoundly rewarding experience, augmenting one’s professional standing while nurturing a communal bond among tech aficionados. Volunteering at TECHSPO serves as a strategic investment in one’s career, underscoring its significance as a valuable allocation of time.
FAQ
What is TECHSPO , and what kind of event is it?
TECHSPO stands as America’s premier tech expo, a showcase of the latest technological advancements. It serves as a platform where industry leaders, innovators, and enthusiasts converge to exchange knowledge and experiences, fostering a collaborative environment.
What are the different types of volunteer roles available at TECHSPO ?
TECHSPO offers a variety of volunteer roles, encompassing registration and check-in teams, support for speakers and VIP guests, technical assistance and setup crews, and roles in social media and content creation. Each position is vital to the event’s success.
How do I become a TECHSPO volunteer, and what’s the application process like?
To volunteer at TECHSPO , one must submit an application detailing qualifications, experience, and availability. The selection process involves a thorough review of applications, with candidates chosen based on their skills and suitability for the event.
What kind of training and preparation do TECHSPO volunteers receive?
Volunteers at TECHSPO undergo extensive training, including pre-event orientation, skills development, and team-building activities. This preparation ensures volunteers are well-equipped to fulfill their roles effectively.
What are the benefits of volunteering at TECHSPO , and how can it impact my career?
Volunteering at TECHSPO offers significant benefits, including resume enhancement, skill acquisition, and networking opportunities with industry leaders. It can also facilitate career advancement and provide a unique perspective on cutting-edge technologies.
What perks and exclusive access do TECHSPO volunteers receive?
Volunteers at TECHSPO enjoy exclusive access to exhibits and demonstrations, complimentary attendance to select sessions and workshops, and TECHSPO swag. They also participate in post-event volunteer appreciation activities and networking opportunities.
How can I make the most of my TECHSPO volunteer experience?
To maximize your experience, be proactive and engage with fellow volunteers, industry leaders, and attendees. Utilize the training and preparation provided, and remain open to learning and embracing new challenges.
What are some common challenges that TECHSPO volunteers face, and how can they be overcome?
Volunteers may face challenges such as time management between duties and personal interests, adapting to last-minute changes, and maintaining energy levels. Overcoming these involves prioritizing tasks, staying flexible, and taking necessary breaks.
How can I sign up for TECHSPO volunteer roles, and what’s the timeline for major events?
To sign up, visit the TECHSPO website and locate the volunteer application section. The timeline for each event varies, but applications typically open a few months in advance, with selections made shortly thereafter.
Can I volunteer at TECHSPO if I have no prior experience in the tech industry?
Yes, TECHSPO welcomes volunteers from diverse backgrounds. While some roles may require technical expertise, others focus on event management, communication, and support. Emphasize your transferable skills and demonstrate a willingness to learn.
Technology Blog
- Scopri l’emozione autentica del wildsino live casino italiano May 3, 2026
- Revelando los secretos dorados de la Auszahlung en Wildsino Casino May 3, 2026
- Descoperă adrenalina și încântarea la Wonaco Casino Site Oficial May 3, 2026
- Unlock Boundless Adventures with Wildsino Casino Welcome Bonus May 3, 2026
- Witamy w krainie szczęścia – odkryj magię casino wonaco May 3, 2026















